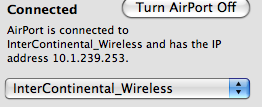
I’m staying at the new Intercontinential San Francisco and partaking of their pay internet services. In the process of using said services, I’ve discovered that they are intercepting and recording every web page I visit. Does that strike anyone else as odd?
 I first noticed that between each page view I would get a little white flash. Then when I went to the New York Times, I discovered that I couldn’t click through to the second page of articles — I would just get redirected back to the first page.
I first noticed that between each page view I would get a little white flash. Then when I went to the New York Times, I discovered that I couldn’t click through to the second page of articles — I would just get redirected back to the first page.
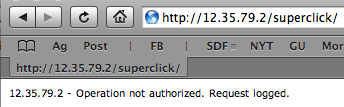
A bit of investigation revealed that Intercontinental Hotel Group is using something called Superclick (and if you don’t believe me, just look at the first testimonial on their homepage). Every time you put in a URL request, the Superclick service uses a transparent proxy to grab the request and redirect it to their own page. Then, from there they do some sort of checking and then perform an HTTP redirect to the actual destination.
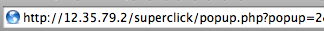
Here is a session:
[zeno@viper ~]$ curl -v http://www.google.com/ * About to connect() to www.google.com port 80 (#0) * Trying 209.85.173.104... connected * Connected to www.google.com (209.85.173.104) port 80 (#0) > GET / HTTP/1.1 > User-Agent: curl/7.16.3 (powerpc-apple-darwin9.0) libcurl/7.16.3 OpenSSL/0.9.7l zlib/1.2.3 > Host: www.google.com > Accept: */* > < HTTP/1.0 302 Moved Temporarily < Server: squid/2.5.STABLE14 < Date: Sat, 01 Mar 2008 07:46:02 GMT < Content-Length: 0 < Location: http://12.35.79.2/superclick/popup.php?popup=6&url=http%3A%2F%2Fwww.google.com%2F < * Closing connection #0
So on every single request they are intercepting the destination, redirecting it, doing something, and then sending you on your way. And of course this breaks some things that use GET and POST variables, although I haven't tested it extensively (and don't really want to). Instead, I setup an SSH tunnel to a tinyproxy server, and told my OS to forward web requests through there. It's working a lot better and I feel a lot safer.
Speaking of safety, I can confirm that this 2005 XSS vulnerability is still present in the Superclick code.
Well, at least their speeds are pretty good. I'm getting 700KB/s on an scp download from Harvard.
Update: In the morning Superclick made me re-login, giving me the opportunity to read their ToS and AUP. Nothing very controversial in there. Using a proxy doesn't violate the terms, and the only vaguely odd terms are those that say you can't "attach[] an excessively long signature to your [email] message," which is just strange, and the one that disallows "forging the headers of your email message in any way," which is over-broad.